Why Password-Based Crypto Wallet Security Is No Longer Enough

The growing risks of password-based protection and how hardware-backed security is changing crypto wallets
Crypto wallet security is evolving.
For years, the standard model has remained the same: protect private keys with a password and store them locally. It is simple, familiar, and widely adopted across nearly every major wallet.
But today, that model is no longer sufficient.
As attacks become more sophisticated and widespread, one thing is becoming clear:
password-based wallet security is the weakest link in crypto.
The Reality: Crypto Losses Are Increasing
The numbers tell a clear story.
- In 2024, wallet drainer attacks stole $494 million from more than 300,000 wallets
- In 2025, total crypto-related losses reached $3.4 billion
- Phishing and credential theft remain among the top causes of wallet compromise
While large exchange hacks dominate headlines, the most consistent losses happen at the user level.
Individual wallets.
And in most cases, attackers are not breaking cryptography.
They are exploiting passwords.
How Password-Based Wallet Security Works
Most crypto wallets today follow a simple approach:
- A user creates a password
- That password encrypts the private keys
- The encrypted wallet is stored on the device
To access funds, the password is required to decrypt the wallet.
This model assumes one critical thing:
that the password remains secure.
If that assumption fails, the entire system fails.
The Core Problem: A Single Point of Failure
Password-based encryption introduces a single point of failure.
If an attacker obtains:
- the encrypted wallet file
- and the password
they can decrypt the wallet offline.
No blockchain interaction is needed. No additional protection exists.
This is why many wallet breaches look different on the surface but share the same root cause.
How Passwords Get Compromised
Passwords are vulnerable in multiple ways.
Phishing Attacks
Attackers create fake wallet interfaces or dApps that look identical to legitimate ones. Users unknowingly enter passwords or recovery phrases.
Malware and Keyloggers
Malicious software captures passwords as they are typed or copied. Crypto-focused malware continues to increase across both Windows and macOS systems.
Credential Reuse
If a password is reused across services, a breach elsewhere can expose wallet access.
Offline Brute Force
If attackers obtain encrypted wallet data, they can attempt millions or billions of password guesses offline.
Weak or reused passwords eventually break.
Real Incidents Highlight the Risk
Several major incidents demonstrate how fragile password-based security can be:
- Atomic Wallet (2023): Over $100 million stolen
- Slope Wallet (2022): Private keys exposed through logging
- LastPass Breach (2022): Encrypted vaults cracked offline, leading to ongoing crypto theft
These events were not failures of blockchain technology.
They were failures of how private keys were protected.
Why This Matters for Cardano Users
Cardano is widely recognized as one of the most secure blockchain architectures.
Its design includes:
- the eUTXO model
- formal verification principles
- peer-reviewed development
However, protocol-level security does not protect against wallet-level weaknesses.
Users can still lose funds due to:
- phishing
- malware
- compromised credentials
Even on a highly secure blockchain, the wallet layer remains critical.
The Industry Shift: Moving Beyond Passwords
The broader technology industry has already started replacing passwords.
PassKeys, developed by the FIDO Alliance and supported by Apple, Google, and Microsoft, introduce a new model.
Instead of relying on a password:
- a cryptographic key pair is generated on the device
- the private key is stored in secure hardware
- authentication happens through biometrics
The secret never leaves the device.
There is no password to remember. No shared secret to steal.
Hardware-Backed Security: A New Approach
Modern devices already include secure hardware components such as:
- Trusted Platform Modules
- Secure Enclave on Apple devices
- Android hardware-backed keystores
These components are designed to:
- generate cryptographic secrets
- store them securely
- prevent extraction by software
This creates a fundamentally different security model.
Instead of protecting keys with something the user knows, security is based on:
something the user has and something the user is.
How Gero Solves the Password Problem
Gero Dashboard removes the need for passwords entirely.
Instead of encrypting private keys with a user-defined password, Gero uses PassKeys combined with the WebAuthn PRF extension to derive encryption keys directly from your device’s secure hardware.
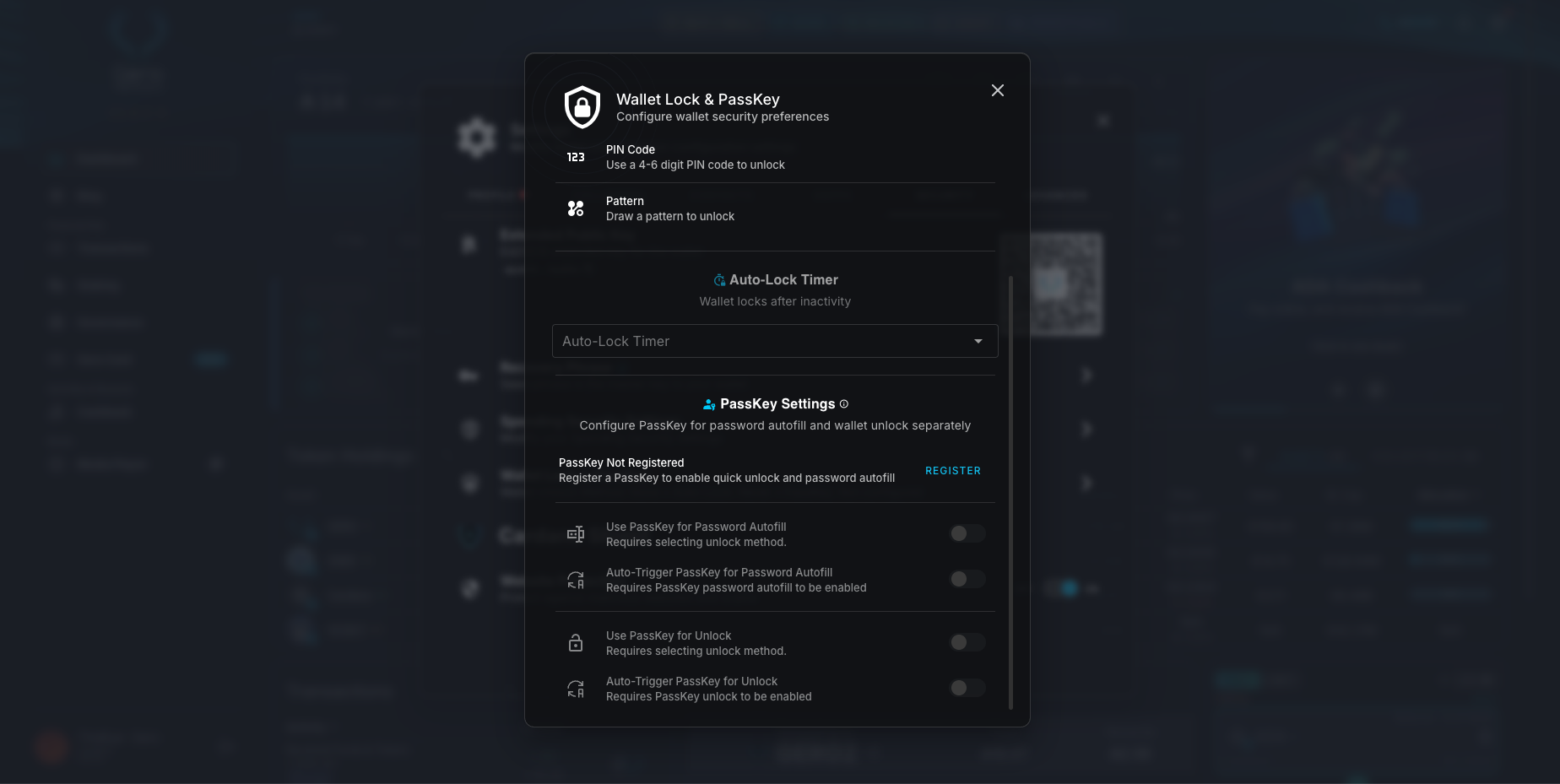
Learn more about Gero’s security approach: https://gerowallet.io/security/
This fundamentally changes how wallet security works.
No Password-Based Encryption
Private keys are never protected by a password.
Hardware-Derived Secrets
Encryption keys are generated inside secure hardware and cannot be extracted or copied.
Biometric Transaction Signing
Sensitive actions require fingerprint or face authentication.
No Secrets Stored in Software
There is no master key stored in browser storage or exposed to applications.
Even if malware is present, it cannot extract the encryption keys.
What Happens When You Sign a Transaction
When using Gero Dashboard:
- The user authenticates with biometrics
- The device generates a hardware-derived encryption key
- The wallet decrypts and signs the transaction
- The key is immediately discarded
There is no reusable secret.
No password to steal.
Security Advantages Over Password-Based Models
No Credential Theft
Without a password, phishing and credential-based attacks are significantly reduced.
No Offline Decryption
Encrypted wallet data cannot be brute-forced without the original device.
Hardware Isolation
Secrets remain protected inside secure hardware components.
Domain Binding
PassKeys are tied to legitimate domains, preventing phishing websites from functioning.
The Evolution of Wallet Security
Crypto wallet security is moving through clear phases.
Phase 1 Password-Based Wallets
Simple but vulnerable.
Phase 2 Hardware Wallets
Highly secure but require additional devices.
Phase 3 Hardware-Backed Software Wallets
Combines strong security with seamless user experience.
This is where the industry is heading.
Why This Shift Matters
Security remains one of the biggest barriers to crypto adoption.
New users are expected to:
- manage complex passwords
- securely store recovery phrases
- understand phishing risks
This creates friction and risk.
PassKey-based systems reduce both.
Authentication becomes faster, simpler, and more secure.
The Bottom Line
Password-based crypto wallet security was a necessary starting point.
But it is no longer enough.
As attacks continue to evolve, relying on passwords introduces avoidable risk.
The next generation of wallet security removes passwords entirely and replaces them with hardware-backed protection.
For users, this means:
- stronger security
- reduced attack surface
- simpler user experience
And for the broader ecosystem, it represents a step toward safer and more accessible self-custody.
